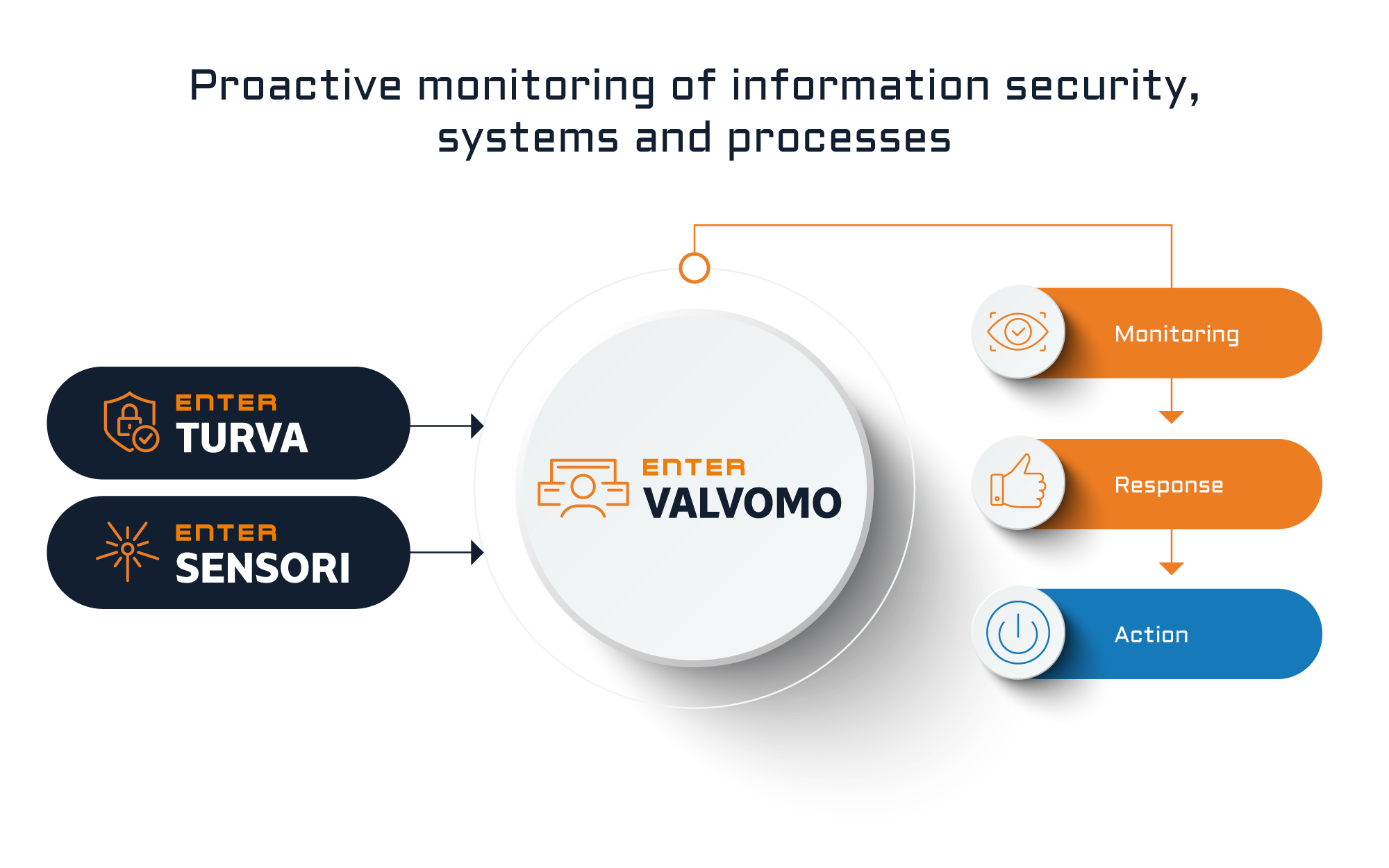
Proactive monitoring and response as a specialist service
Enter Valvomo supplements automatic IT environment monitoring with Enter specialists’ service work. The key benefit is a real-time situational picture and actions based on it.
With the service, your organisation’s IT infrastructure and its critical points are covered by proactive monitoring. Enter Valvomo supports both local data centre environments and cloud or hybrid environments.
Enter Turva + Enter Valvomo
The core of the Enter Turva + Enter Valvomo service package is your organisation’s information security. The Enter Turva service protects data, hardware and users from cyber-threats. Together with Enter Valvomo, the service package includes technical data security and also monitoring and response by Enter specialists.
Enter Sensori + Enter Valvomo
The core of the Enter Sensori + Enter Valvomo service package is the undisturbed and seamless operation of IT systems and processes. The Enter Sensori service provides notifications of disturbances it detects in IT systems and processes. Together with Enter Valvomo, the service package includes technical monitoring and also human monitoring and response by Enter specialists.
Customisable Enter Valvomo
In addition to standardised Enter Valvomo services, we implement solutions customised for individual customer needs.
We can adapt our services to your organisation’s needs, according to the operational environments and the targets to be monitored and their criticality – for example, in terms of response times and jointly agreed processes.